The Great Rewrite: From C/C++ Spaghetti to Memory-Safe Rust Microservices
The Great Rewrite: From C/C++ Spaghetti to Memory-Safe Rust Microservices
How DARPA TRACTOR, AI Agent Teams, and Regulatory Pressure Are Forcing the Largest Code Migration in History
The Ticking Clock on Unsafe Code
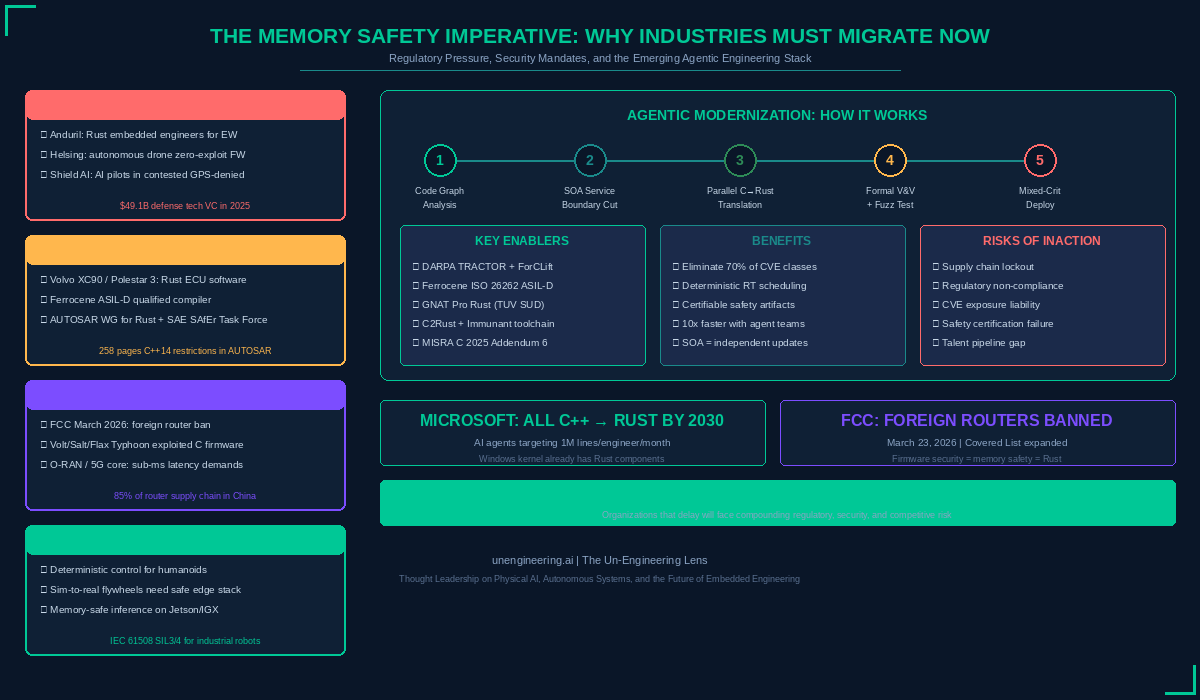
Seventy percent of all disclosed security vulnerabilities in large systems trace back to a single root cause: memory-unsafe code written in C and C++. Buffer overflows, dangling pointers, use-after-free exploits — these are not edge cases. They are the dominant attack surface across defense platforms, automotive ECUs, telecommunications infrastructure, and the embedded systems that underpin Physical AI. The industry consensus is no longer debatable: bug-finding tools alone cannot fix what is fundamentally a language-level problem.
Yet the global installed base of C and C++ code is measured in the hundreds of billions of lines. It runs everything from fighter jet avionics to the router sitting in your home. Rewriting it manually is economically impossible. This creates the central tension of embedded systems engineering in 2026: the code must change, but the scale defies human effort alone.
The convergence of three forces — regulatory mandates, AI-powered code translation, and the maturation of Rust for safety-critical systems — is now making the previously impossible migration not just feasible but inevitable. This article examines the state of that migration, its most promising R&D pathways, and a realistic vision of how agentic AI engineering can execute it at scale.
DARPA TRACTOR: The Moonshot for Automated Translation
In August 2024, DARPA launched the Translating All C to Rust (TRACTOR) program — an explicit acknowledgment that the Department of Defense itself depends on legacy C systems it can no longer afford to leave unprotected. The program’s ambition is to automate the translation of C code into idiomatic, memory-safe Rust that matches what a skilled human developer would produce.
TRACTOR is not a theoretical exercise. By mid-2025, DARPA awarded a $5 million grant to a multi-university consortium — Illinois, Wisconsin-Madison, UC Berkeley, and Edinburgh — to develop ForCLift (Formally-Verified Compositional Lifting of C to Rust), an approach that combines formal methods, program analysis, and LLMs to produce translations with mathematical correctness guarantees. The tool company Immunant, which maintains the C2Rust transpiler, is also a key contributor, providing the foundational static-analysis infrastructure.
DARPA program manager Dan Wallach has been candid: current LLMs can already produce reasonable C-to-Rust translations for straightforward code, but struggle with the complex pointer arithmetic, undefined behavior exploitation, and deeply coupled state that characterize real-world embedded systems. The research challenge is to close that gap for the hardest 20% of constructs that cause 80% of the vulnerabilities. MIT Lincoln Laboratory is independently evaluating all TRACTOR submissions against production-grade codebases.
Beyond Translation: SOA Decomposition and Mixed-Criticality Microservices
A line-by-line translation of monolithic C into monolithic Rust misses the architectural opportunity. The real prize is decomposing legacy “spaghetti” codebases into a Service-Oriented Architecture (SOA) of independently deployable, independently testable microservices — each assigned an explicit criticality level.
In the automotive domain, ISO 26262 defines Automotive Safety Integrity Levels from QM (no safety requirement) through ASIL-D (highest). The cost of verification and certification scales exponentially with ASIL level. Mixed-criticality architectures exploit this by isolating the smallest possible ASIL-D kernel — a brake actuator control loop, for instance — from ASIL-B sensor fusion pipelines and QM infotainment services. Each service runs with guaranteed worst-case execution time (WCET) budgets enforced by the underlying RTOS or hypervisor, such as PikeOS or QNX.
Rust is uniquely suited for this decomposition. Its ownership model enforces memory isolation at compile time, eliminating entire classes of inter-service data corruption. The AUTOSAR consortium established a dedicated Rust Working Group in 2022, and Eclipse SDV’s S-CORE project already provides a Rust-based async runtime orchestrator targeting safety-critical automotive middleware. The SAE International’s SAfEr Rust Task Force is concretizing ISO 26262 guidelines specifically for Rust, including language subsetting and evidence generation.
Neo Defense Tech: Where Memory Safety Is a Matter of National Security
Defense technology startups raised a record $49.1 billion in venture capital in 2025, nearly doubling the prior year. The leaders — Anduril ($30.5B valuation), Helsing (€12B), Shield AI, Saronic — are building autonomous systems where a single memory corruption exploit could compromise a weapons platform, a reconnaissance drone swarm, or an electronic warfare asset.
Anduril is already hiring embedded Rust engineers specifically for electronic warfare platforms running on NixOS and bare-metal RTOS environments. Their Lattice system-of-systems architecture integrates autonomous drones, counter-UAS defenses, and underwater vehicles — all surfaces where a buffer overflow is not a bug report but a potential mission failure. Helsing’s mass-produced HX-2 strike drones and Europa autonomous fighter jet demand firmware that is provably free of memory safety vulnerabilities before it reaches the battlefield.
The shift from C/C++ to Rust in defense is not aspirational — it is operational. When your autonomous system operates in contested, GPS-denied airspace under adversarial electronic attack, every undefined behavior in your firmware is an exploitable surface. The DARPA TRACTOR program exists precisely because the DoD recognizes that its own legacy codebases are among the most critical and most vulnerable.
The FCC Router Ban: A Wake-Up Call for Firmware Security
On March 23, 2026, the FCC added all foreign-produced consumer-grade routers to its Covered List, effectively banning new models from entering the U.S. market. The decision followed an interagency determination that foreign-manufactured routers pose unacceptable national security risks, citing their exploitation in the Volt Typhoon, Salt Typhoon, and Flax Typhoon cyberattacks that targeted U.S. critical infrastructure.
The immediate market impact is sweeping: virtually every major router brand — TP-Link, ASUS, Netgear, Linksys, even Google Nest WiFi — manufactures overseas. But the deeper signal is about firmware security. These state-sponsored attacks exploited memory-unsafe C firmware running on commodity SOHO routers to build botnets that targeted power grids and water systems. The routers were not compromised through sophisticated zero-days; they were compromised through the same buffer overflows and memory corruption vulnerabilities that have plagued C code for decades.
For the broadband access market, the implication is clear: any manufacturer seeking FCC “Conditional Approval” to re-enter the U.S. market must demonstrate a credible security posture. Firmware written in memory-safe Rust, with automated vulnerability scanning and formal verification, becomes a competitive differentiator — and eventually a regulatory requirement. This is industrial policy wrapped in security language, and it will reshape the entire networking equipment supply chain.
The Agentic Future: AI Engineer Teams Modernizing Legacy Code at Scale
In February 2026, Anthropic demonstrated that a team of 16 AI coding agents, working in parallel across nearly 2,000 sessions, could produce a 100,000-line Rust-based C compiler from scratch — one capable of building Linux 6.9 across x86, ARM, and RISC-V architectures. The total API cost was approximately $20,000. This was not a toy demo; the compiler passes the GCC torture test suite and can compile production software including FFmpeg, SQLite, PostgreSQL, and Redis.
Microsoft has announced its intent to eliminate all C and C++ code from its major codebases by 2030, using AI agents capable of refactoring at a target rate of one million lines per engineer per month. The Windows kernel already contains Rust components.
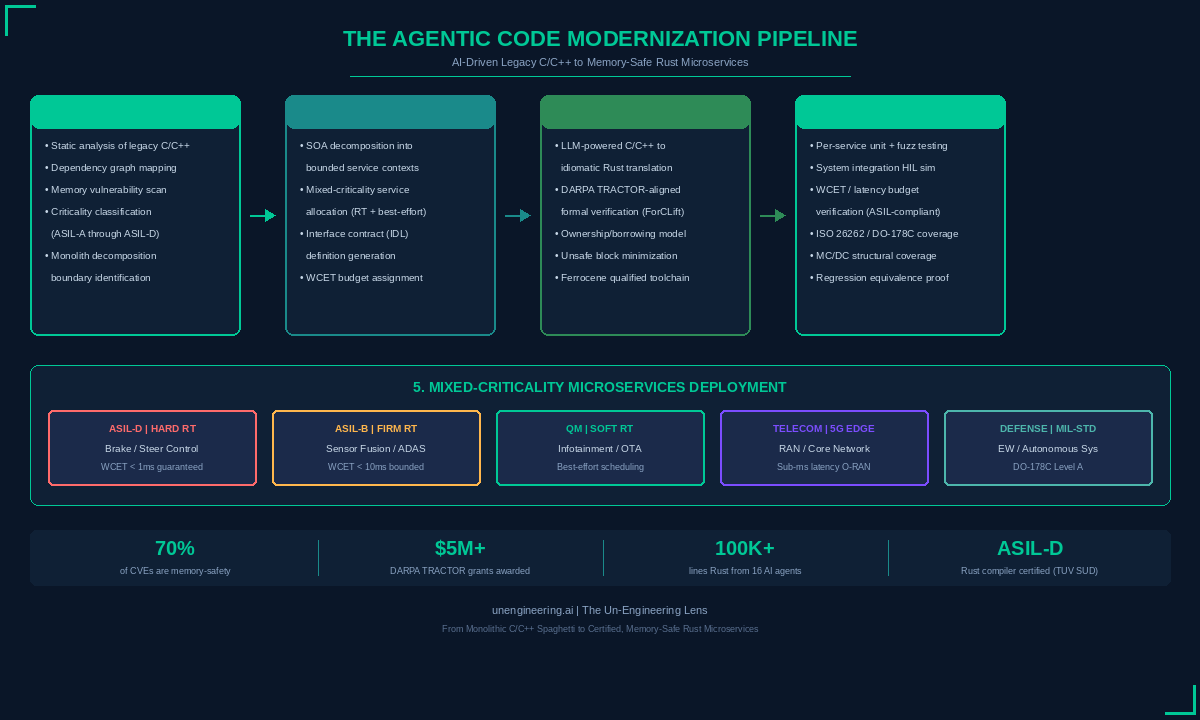
Now project this capability onto the embedded systems modernization challenge. Here is a realistic near-term scenario:
Scenario: Agentic Modernization of an Automotive ECU Stack
Phase 1 — Discovery Agents analyze a 500,000-line monolithic C codebase controlling powertrain, ADAS sensor fusion, and body electronics. They generate a complete dependency graph, classify each function by its safety criticality (ASIL-A through ASIL-D), identify memory-unsafe patterns, and propose service boundaries for SOA decomposition.
Phase 2 — Architect Agents partition the codebase into 40–60 bounded microservices with explicit interface contracts (IDL definitions), WCET budgets per service, and middleware mapping to AUTOSAR Adaptive or DDS transport. Hard real-time brake and steering control becomes a 5,000-line ASIL-D Rust service; sensor fusion becomes an ASIL-B service; infotainment becomes QM.
Phase 3 — Translator Agents work in parallel, each assigned a service. Using TRACTOR-aligned translation pipelines (ForCLift formal verification, C2Rust transpilation, LLM-driven idiomization), they produce safe, idiomatic Rust for each service. Unsafe blocks are minimized and explicitly justified. The target toolchain is the Ferrocene ASIL-D qualified Rust compiler or AdaCore’s GNAT Pro for Rust, certified by TUV SUD.
Phase 4 — Validation Agents execute per-service unit testing, fuzz testing (cargo-fuzz), and formal equivalence checking against the original C behavior. System-level Hardware-in-the-Loop (HIL) simulation validates end-to-end timing, fault injection response, and WCET compliance. MC/DC structural coverage is generated automatically for ISO 26262 Part 6 evidence packages. Regression suites prove behavioral equivalence with the legacy system.
Phase 5 — Deployment targets a mixed-criticality runtime (PikeOS, QNX, or seL4-based hypervisor) where each Rust microservice runs in its own partition with time and memory isolation. Services communicate via zero-copy shared memory or DDS, with deterministic scheduling guarantees. OTA updates can target individual services without revalidating the entire system.
The benefits are transformative: elimination of 70% of vulnerability classes at the language level; independent deployment and testing of each service; dramatically reduced certification costs through criticality decomposition; and a modernization timeline measured in months rather than years. What previously required a team of 50 embedded engineers working for three years becomes a coordinated AI agent operation with human architects providing oversight, domain constraints, and final sign-off.
Industry Reflections: Where the Migration Hits Hardest
Physical AI and Robotics
Humanoid robots and autonomous mobile platforms demand deterministic control loops executing on edge compute hardware — NVIDIA Jetson Orin, IGX, or custom RISC-V SoCs. These are mixed-criticality systems by nature: a safety-critical motor controller must coexist with a best-effort VLA inference pipeline. Rust’s compile-time memory guarantees eliminate an entire class of runtime failures in the control layer, while its zero-cost abstractions match C’s performance envelope. For Physical AI companies building sim-to-real data flywheels, memory-safe edge stacks are not a nice-to-have — they are a prerequisite for IEC 61508 certification.
Autonomous Vehicles and ADAS
The automotive industry is moving fastest. Volvo’s XC90 and Polestar 3 already run Rust-based ECU software in production. Ferrous Systems and AdaCore offer ISO 26262 ASIL-D qualified Rust toolchains. The AUTOSAR Rust Working Group and SAE SAfEr Task Force are building the standards infrastructure. For ADAS systems processing LiDAR, radar, and camera fusion at 30+ FPS with hard latency constraints, Rust’s ownership model provides the memory safety that MISRA C guidelines attempt through 258 pages of restrictions — but enforce at the compiler level rather than through human discipline.
Telecommunications
The FCC’s March 2026 router ban is the most visible symptom of a deeper problem: telecommunications infrastructure runs on billions of lines of C code with known memory safety vulnerabilities. The O-RAN Alliance’s push toward disaggregated, software-defined 5G RAN introduces microservices architectures that demand sub-millisecond latency and deterministic scheduling — precisely the mixed-criticality profile where Rust excels. As 5G Advanced and 6G edge architectures distribute compute across the network, the firmware security of every node becomes a systemic risk. The Typhoon campaigns proved that state actors will exploit memory-unsafe router firmware at scale.
The Verdict
The migration from C/C++ to Rust is no longer a technical curiosity or a language-community aspiration. It is a regulatory, security, and operational imperative converging across every industry that depends on embedded systems. DARPA is funding it. Microsoft is committing to it. The FCC is creating market conditions that demand it. Defense primes are hiring for it. Automotive OEMs are shipping it.
The remaining question is not whether to migrate, but how fast your AI agent teams can execute it. Organizations that treat this as a five-year planning exercise will find themselves facing compounding regulatory non-compliance, uninsurable CVE exposure, and a talent pipeline that has already moved on to Rust. The agentic modernization pipeline outlined here is not science fiction — the components exist today, and the economics of AI-driven translation are improving monthly.
The great rewrite has begun. The only variable is who leads and who follows.